In the digital realm, your domain name is akin to your online street address. It pins down your website, making it easily accessible to visitors. However, this crucial piece of your online identity can fall prey to a malicious act known as domain hijacking. This insidious attack occurs when hackers usurp your domain name without your consent, effectively stealing your web presence.
The consequences of domain hijacking can be devastating. Your website may suddenly become inaccessible to users, redirecting them to a fraudulent site. Cybercriminals could spread malicious content through phishing schemes or malware distribution, tarnishing your reputation and potentially exposing sensitive user data. It's crucial to understand the methods employed by hijackers and take proactive steps to safeguard your online identity.
- Protecting Your Domain from Hijacking
- Understanding the Warning Signs of a Hijacking Attempt
- Recovery Strategies for Your Stolen Domain
Hacked Domains: A Gateway to Cybercrime
A domain name, once a simple identifier on the vast expanse of the internet, has evolved into a high-value target in the world of cybercrime. Hacked domains, often unsuspecting victims of sophisticated attacks, provide criminals with a stealthy platform to launch their malicious operations. By seizing control of legitimate websites or creating fraudulent replicas, attackers can deploy malware, trick individuals into sharing credentials, and promote harmful content.
- Users may unknowingly land on these malicious websites through compromised search engine results or links shared on social media.
- Attackers can exploit vulnerabilities in website software to gain unauthorized access and execute their malicious code.
- Combating this threat requires a multi-pronged approach involving vigilance from users, robust security measures by website owners, and continuous efforts by cybersecurity professionals.
Vigilance and collaboration are essential in safeguarding our online presence against these malicious actors.
Malware Threats: Hidden Dangers on Your Computer
The digital world offers incredible opportunities, however it also harbors unseen dangers. Among these threats, malware infections pose a particularly insidious risk, silently infecting your system and compromising your valuable data. These malicious programs can infiltrate your devices through a variety of means, including infected emails. Once inside, malware can spread rapidly, performing harmful tasks that range from data theft to system corruption.
It's crucial to be aware of the threats posed by malware and take proactive steps to safeguard yourself. This encompasses staying informed about common vulnerability vectors, practicing safe browsing habits, implementing robust antivirus software, and periodically backing up your important data.
Safeguard Your Inbox from Malicious Messages
In today's digital age, spam emails have become a pervasive nuisance. These unsolicited and often malicious messages can flood your inbox, wasting your time and potentially exposing you to security threats. Fortunately, there are several robust strategies you can implement to combat spam and secure your email account.
Utilize strong passwords that include a mix of uppercase and lowercase letters, numbers, and symbols. Avoid using the same password for multiple accounts. Regularly update your email software to patch any vulnerabilities that spammers could exploit.
- Be cautious when opening emails from unknown senders or clicking on suspicious links.
- Report spam emails to your email provider to help them identify and block future cybercriminals.
By following these precautions, you can significantly reduce the amount of spam that reaches your inbox, creating website a more secure and productive email experience.
A Sinister Alliance: Stolen Domains and Phishing Attacks
Phishing attacks are a common threat in the online world, with attackers often using fraudulent tactics to trick users into revealing sensitive information. Seized domains add an another layer of danger to this already serious problem. Attackers can acquire legitimate domains and use them to create realistic phishing pages. This makes it even more difficult for users to distinguish real sites from fakes, leading to a greater risk of falling victim to these attacks.
Moreover, stolen domains can be used to spread malware and launch other cybersecurity threats. Users who visit a compromised site may unknowingly download malicious software onto their devices, compromising their security and privacy.
- To mitigate the risk of falling victim to phishing attacks that use stolen domains, it is essential to be aware when clicking on links or providing information online.
- Frequently check for domain legitimacy by looking at the URL and the website's security certificate.
- Employ a reputable antivirus software to defend your devices from malware.
Beneath the Surface: Malware and Domain Ownership
While domain ownership can be a valuable asset for individuals and businesses alike, it's crucial to recognize the lurking threats that come with it. Cybercriminals often exploit domains for nefarious purposes, spanning the distribution of malware and spam to more sophisticated attacks like phishing and DNS spoofing.
A compromised domain can be weaponized to deliver malicious payloads, ultimately leading to data breaches, financial losses, and reputational damage. Vulnerable domains become easy targets for malware distributors, who can exploit weaknesses in their systems to gain control and launch attacks.
- Domain hijacking: Thieves seize legitimate domains, redirecting traffic to malicious sites.
- Malvertising: Domains are infected with ads that deliver malware or track user activity.
- Phishing: Fake domains mimic legitimate ones to trick users into revealing sensitive information.
Therefore, it is essential for domain owners to take proactive steps to protect themselves and their users. This includes implementing robust security protocols, implementing multi-factor authentication, and staying informed the latest threats.
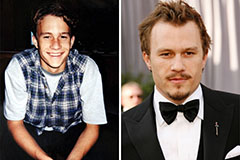 Heath Ledger Then & Now!
Heath Ledger Then & Now! Jennifer Love Hewitt Then & Now!
Jennifer Love Hewitt Then & Now! Danny Pintauro Then & Now!
Danny Pintauro Then & Now! Elisabeth Shue Then & Now!
Elisabeth Shue Then & Now! Naomi Grossman Then & Now!
Naomi Grossman Then & Now!